Impersonating Attack
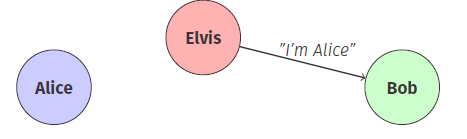
How the Attack Works
: “I’m Alice”
where E(A) means Elvis is impersonating Alice.
A simple protocol - Symmetric Key Encryption
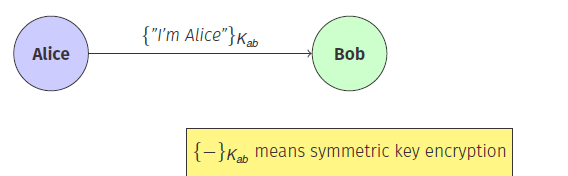
Owning Shared Keys
If Alice and Bob share a key then Alice can encrypt the message.
Replay of Messages
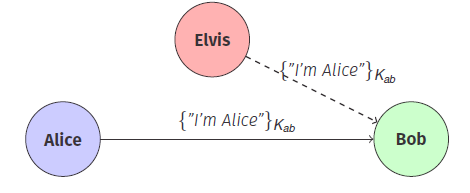
How the Replay Attack Works
A Simple Protocol - Nonce
Number that is only used once (often used in a challenge/response setting).
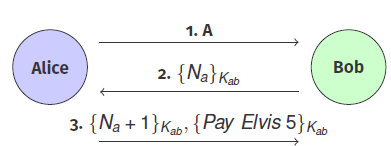
Protocol steps :
Another example :
Exploitation
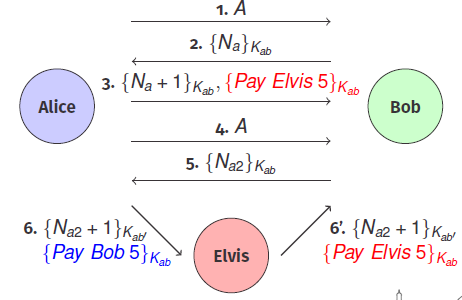
Better Protocol - Fixed
What Bob Can Be Sure Of :
- He is talking to Alice.
- Alice wants to send Elvis €5.
- Alice’s messages are fresh (not replayed).