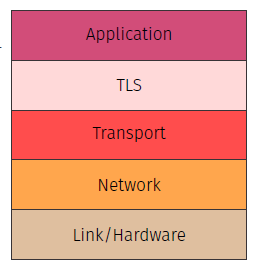
The TLS layer runs between the Application and Transport layer. The encryption is transparent to the Application layer. Normal TCP and IP protocols etc. can be used at the low layers.
The TLS protocol
TLS Handshake : Establishing a Secure Connection
Key Exchange Options :
- RSA : Client encrypts pre-master secret with server’s public key.
- Diffie-Hellman : Client and server derive a shared secret. After the handshake, all communication is encrypted using the negotiated symmetric key.
Handshake in Alice and Bob
TLS Handshake Steps
Hash Computation :
Session Key Generation :
Mapping TLS Message Flow to Cryptographic Representation
clientHello ()
- Textual : Client sends a random nonce and supported cipher list.
- Mathematical :
- is the client’s none, used in key derivation and preventing replay attacks.
serverHello + Certificates ()
- Textual : Server responds with a random nonce and chosen cipher suite.
- Server sends it certificates (signed by CA).
- Mathematical :
- is the server’s random nonce, and is the server certificate containing its public key.
Key Exchange ()
- Textual : Client encrypts a pre-master secret with the server’s public key.
- Mathematical :
- : The pre-master secret encrypted with the server’s public key.
- ensures integrity and is encrypted using the session key .
Server Verifies and Responds ()
- Textual : Server verifies handshake and confirms key agreement.
- Mathematical :
- is computed over handshake data, confirming mutual agreement.
Key Derivation
- Textual : Both sides derive the session key using nonces and exchanged key material.
- Mathematical :
- is a Key Derivation Function (KDF) that combines , and to generate .
Weaknesses in TLS
Configuration Weaknesses :
- Cipher Downgrading (forcing weaker ciphers)
- Self-Signed Certificates (no trusted authority)