Question
If Alice and Bob know each other’s public keys, can they set up a symmetric key ?
- Public Key Encryption Notation means public key encryption.
- and can then be used to generate a symmetric key.
Message Guarantees
Goal : Alice and Bob are sure they are talking to each other.
- Whoever could know is the person who decrypted the first message
- Whoever could know is the person who decrypted the second message.
Man-in-the-Middle Attack on Needham-Schroeder
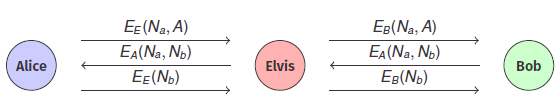
How the Attack Works
- Alice sends to Elvis, BUT Elvis then forwards this to B pretending to be A : .
- Bob responds with , thinking he’s talking to Alice, BUT Elvis forwards this to Alice.
- Alice now sends to Elvis, so Elvis now has Bob’s nonce AND forwards it to B to complete the protocol.
- Now Elvis can impersonate Alice and Bob.